Advanced cryptography (as defined by the National Cyber Security Centre) refers to various techniques that deploy cryptographic methods to offer data-processing functionality that exceeds what can be achieved via traditional cryptographic functions. These approaches differ in their level of computational complexity and include techniques in which multiple parties work together to process data but want to keep some of their information secret.
Applications of advanced cryptography include data protection, the creation of digital signatures, securing communications and blockchain technology. The latter relies on cryptographic techniques to maintain the integrity of distributed ledgers and secure transactions.
Different Advanced Cryptography Techniques
Examples of advanced cryptography techniques include homomorphic encryption, quantum cryptography and post-quantum cryptography. The first of these makes it possible to perform computations on encrypted data without first decrypting it, thereby ensuring privacy is preserved. Those with an interest in this sphere, such as Domen Zavrl, understand that homomorphic encryption may be used in secure multiparty computation, cloud computing and machine learning where privacy is important.
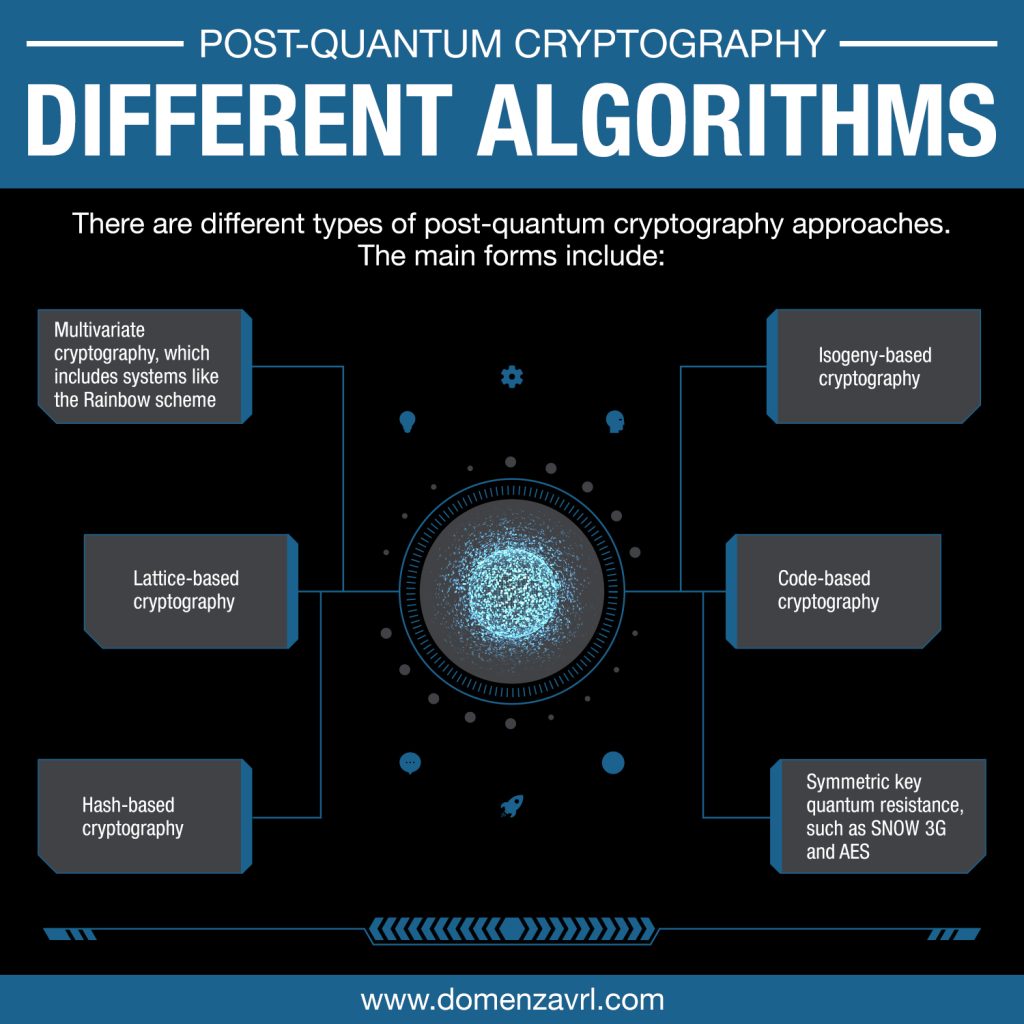
Post-quantum cryptography focuses on developing encryption algorithms able to resist attack from the quantum computers of the future. These techniques include code-based cryptography, lattice-based cryptography and hash-based cryptography.
Other advanced cryptography techniques are zero-knowledge proofs, private set intersection, private information retrieval and attribute-based encryption. The latter limits the decryption of messages to those who possess a specific set of attributes.
When Should Advanced Cryptography Be Used?
If an organisation is seeking a solution for a secure data processing issue, advanced cryptography could be the answer. This is especially the case where multiple parties need to work together to achieve the desired outcome, there’s no trusted third party to perform the operation, an increase in overhead costs are acceptable, and there’s a chance a small number of the parties involved may act dishonestly or be unreliable.
Identifying Possible Solutions
To decide upon the most appropriate cryptographic solution, an organisation should consider how the problem is currently being tackled (and whether this is actually sufficient), whether trust between parties could be improved, if a solution could be designed using traditional cryptographic methods, and which advanced cryptography techniques could solve an aspect of the issue in a way that traditional approaches cannot. It’s also important to think about any restrictions that using advanced cryptography could impose, and the cost of the entire solution should be assessed.
For more information about advanced cryptography, take a look at the embedded PDF.


Recent Comments